As AI continues to dominate the broader internet landscape, users have begun asking questions about the legitimacy of their interactions online. In this episode, our expert talks to us about what it was like to build social media bots that, on the one hand, helped his clients gain millions of…
The recent enforcement of the TikTok ban (prior to its temporary reversal by President Trump) has left many wondering about the risks posed by the popular social media app. Sure, TikTok is owned by a Chinese company, but how dangerous is this really to national security and our data privacy?…
As we reach the end of the Holiday season, individuals are more likely to be reactive as opposed to proactive in how they treat their online activity. That’s why we reached out to Phil Reitinger to discuss a few crucial steps to keep your cybersecurity at the forefront of your…
What Are the Real Benefits of Zero-Trust Security? In the modern cybersecurity landscape, zero-trust approaches to security have become popular for organizations looking to protect valuable data. But why has this approach not made its way to individual cybersecurity protections—that is, why is this approach more valuable to organizations and…
As the utilization of artificial intelligence becomes increasingly prevalent, it is no surprise that AI plays an enormous role in both cyberattacks as well as cybersecurity. However, exactly how AI works in cybersecurity is rarely discussed: what are the benefits of artificial intelligence integration, and how does this combat the…
Consumers of every stripe are told that deploying home cybersecurity protection measures is an important component of good cyber hygiene. But despite the importance of cybersecurity protection, we rarely stop to ask ourselves: What do we need our cybersecurity to protect? As a result, most home cybersecurity protection is grounded…
When it comes to choosing organizations to share your personal data with, it can often feel like your options are few and far between. This is because many of the services we use (such as healthcare) require the consenting exchange of personal data. However, just because your data must be…
With the overwhelming number of bad actors looking to profit off your personal information, it can often feel like there is no way to protect your data privacy. However, just because you are a target by cybercriminals does not mean that you cannot take proactive steps to guard against attacks.…
Responsible for securing institutions, all the way from colleges to banks, multi-factor authentication is a layered approach to securing individuals’ data. Yet despite its importance, many users do not understand the principles behind multi-factor authentication or how it differs from the ubiquitous two-factor identification. In this episode, we will discuss…
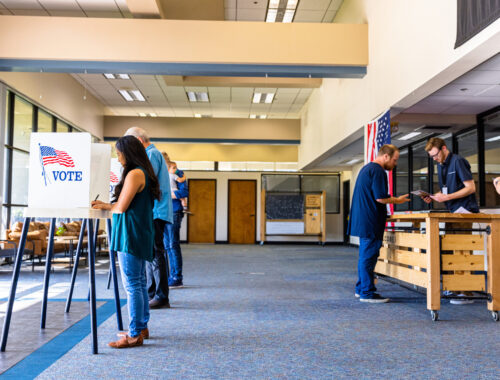
With the Cambridge Analytica scandal of 2016, the role of voter information was suddenly thrust into the political spotlight. In the years since, we have become increasingly aware of the ways in which our voter files can be manipulated and sold to the highest bidder. But what is a voter…