As AI continues to dominate the broader internet landscape, users have begun asking questions about the legitimacy of their interactions online. In this episode, our expert talks to us about what it was like to build social media bots that, on the one hand, helped his clients gain millions of…
More than any other industry, manufacturing takes the brunt of ransomware attacks—and these hacks do not appear to be slowing down. In combination with the other most-hit industries (e.g., professional, scientific and technical services), ransomware attacks against these sectors accounted for more than 40% of all 2024 incidents. For those…
In previous issues of MyIDMatters, we have discussed the vast differences between the data protection policies of each of the 50 states (assuming such policies even exist!). We have noted that, despite the success of larger frameworks like the European Union’s cyber policy, there are no comprehensive federal laws in…
Those of us who have seen the Godfather are familiar with the concept of the “Five Families of Crime.” However, very few of us know that there is a “Five Families of Crimeware.” One of these organizations has been linked to a string of recent cybersecurity attacks leading to millions…
How well-positioned are corporations to protect consumer data? This question is on the minds of many analysts as cyberattacks become increasingly prevalent with the aid of artificial intelligence. These attempted breaches are stress-testing organizations who are tasked with safeguarding personal data, and they are also putting CISOs in uncomfortable positions.…
With the expiration of the Cybersecurity Information Sharing Act (CISA) of 2015 on the horizon, House intelligence committees have recently received briefings on the efficacy of the law, detailing to what extent private businesses have been willing to share cyber threat data with the government. However, new developments have placed…
These days, innocuous bits of personal information can be used to protect—or compromise—your cybersecurity. What may astonish readers to learn is that your postal code information is currently being used to strengthen fraud protection against cyberattacks. Having been embedded in e-commerce systems, identity verification checks and logistics operations, postal codes…
This story has far-reaching implications that could affect every walk of life: the personal information of millions of schoolchildren has been put at risk after the successful hacking of PowerSchool, the developer of a widely used education tech program. The company’s Student Information System (SIS) is a digital platform that…
The newly establish Department of Government Efficiency (DOGE) has created quite the stir in Washington, causing legal experts to speculate that the organization has violated the Privacy Act as well as various cybersecurity laws. By taking control of the Treasury Department’s central payments database, they argue, DOGE has created an…
Although this story occurs outside of the United States and United Kingdom, it details governmental cybersecurity actions that should concern citizens everywhere. The Turkish government is proposing a law to empower their recently conceived Cybersecurity Directorate. Prior to this proposal, Turkey mirrored the United States by lacking comprehensive federal cybersecurity…
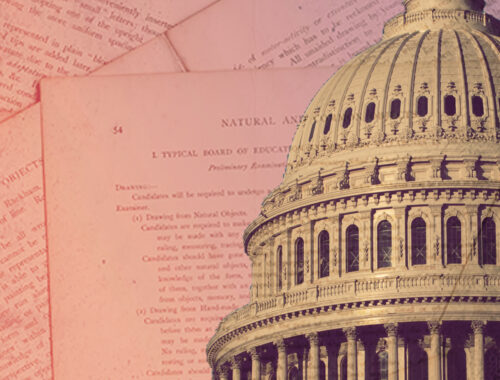
Poised to radically disrupt the generative AI space, the Chinese startup, DeekSeek, sent shockwaves across global economic markets after debuting its R1 AI assistant in January. As a reasoning model, DeepSeek is fed a myriad of data by its parent company, High-Flyer, so that it can train itself to better…
It appears the notorious ransomware group, LockBit, is back on the scene after making headlines as the most ubiquitous form of ransomware in 2022. With double extortion tactics and an ability to work around traditional security measures, this Ransomware-as-a-Service (RaaS) model is deceptive, effective and able to distribute malware at…
With every new presidential administration comes a new approach to federal policy—and this includes new approaches to cybersecurity protections. In the wake of the January inauguration, the question on many cybersecurity experts’ minds is: what should we expect from the Trump administration? Will previous strategies continue to be employed, or…
The recent enforcement of the TikTok ban (prior to its temporary reversal by President Trump) has left many wondering about the risks posed by the popular social media app. Sure, TikTok is owned by a Chinese company, but how dangerous is this really to national security and our data privacy?…